Professional Portfolio
Highlighting my skills, certifications, and ongoing learning in cybersecurity.
Technical Skillset:
Security Analysis & Monitoring: SIEM/SOAR Analysis (Splunk, QRadar, Elastic Security), Log Correlation & Analysis (Windows, Linux, Cloud), Network Traffic Analysis (Wireshark, Nmap, Tcpdump), Intrusion Detection/Prevention (Suricata/Snort, Zeek).
Incident Response & Threat Management: Incident Handling & Escalation, Threat Intelligence Utilization, Vulnerability Assessment (Kali Linux, OpenVAS, Nessus), Risk Assessment & Mitigation, Basic Digital Forensics.
Security Operations & Compliance: NIST CSF, MITRE ATT&CK Framework, Security Policy Development & Implementation, Playbook/Workflow Management & Development, Network & Cloud Security (AWS/Azure/GCP), Compliance (ISO 27001, SOC 2).
Scripting & Automation: Python Scripting for Security Tasks, PowerShell & Bash Scripting, Automation of Log Analysis & Incident Response.
Cloud Security: Cloud Platform Security (IAM, Security Groups), Cloud Logging & Monitoring, Cloud Security Posture Management (CSPM).
SHA256: d79bdf208cd307c3ddbd055d344f22d71f9727d4818e438a5a6f71acd6c7f121
MD5: ba649261d8aa827e48c9ff4d4bbd1075
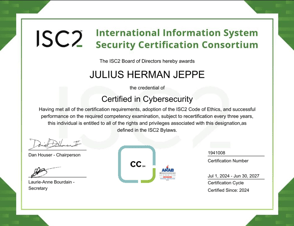
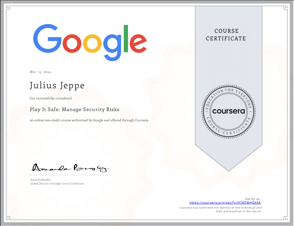
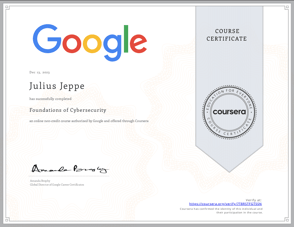
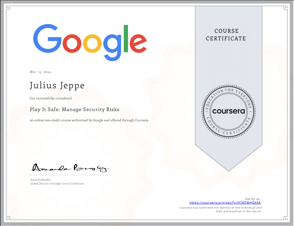
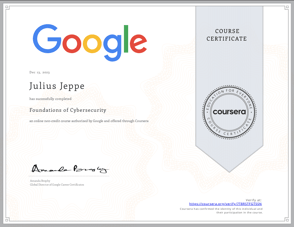
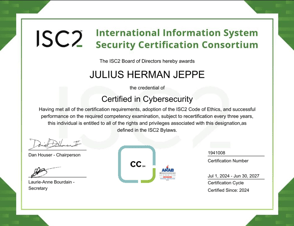
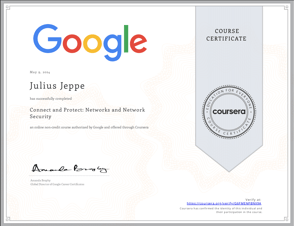
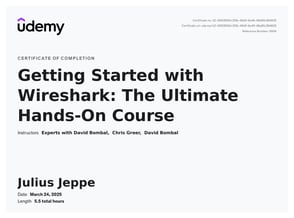
Professional Certifications
Currently, I have achieved the following Certifications:


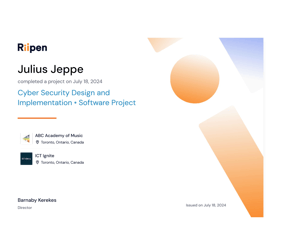


Professional Development
Showcasing past, current, and Ongoing Projects


Project & Evaluation Space
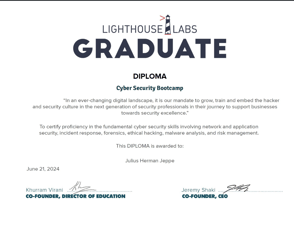
Throughout the Lighthouse Labs cybersecurity program, I engaged in twelve diverse projects, each designed to solidify practical skills and deepen my understanding of core cybersecurity principles. These projects ranged from foundational exercises in network security and vulnerability scanning to more complex tasks involving incident response and threat detection. I honed my scripting abilities with Python and BASH, automating security tasks and analyzing log data. Projects aligned with industry standards like NIST and ISO, providing real-world context for theoretical concepts. Culminating in a comprehensive capstone project, I applied the accumulated knowledge to simulate a realistic cybersecurity scenario, demonstrating my ability to analyze, mitigate, and report on complex security incidents, effectively showcasing my readiness for a career as a Cybersecurity Analyst or Incident Responder.
My Project-XY cybersecurity homelab, built using VirtualBox, provides a realistic, hands-on learning environment by simulating a small enterprise network. It features a Windows Server 2025 Domain Controller, an Ubuntu Server 22.04 Email Server, and dedicated Ubuntu 22.04 Security Servers and a Security Playground. To mimic typical user activity, Windows 11 and Ubuntu Desktop 22.04 workstations are included, while a Kali Linux 2024.2 attacker machine enables offensive security practice. This setup allows me to utilize a variety of security tools, including Wazuh, Postfix, Evil-WinRM, Hydra, and Security Onion, for practical experience in network administration, security monitoring, vulnerability assessment, penetration testing, and the simulation of both cyberattacks and defensive measures, solidifying my cybersecurity skills in a controlled environment.


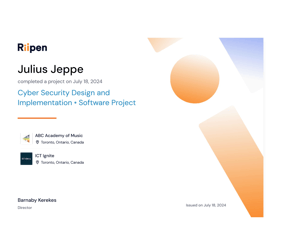
This project centers on establishing robust and scalable security for ABC Academy's Hinna software, a small business management platform handling sensitive client data, scheduling, and billing. The endeavor involves a comprehensive security overhaul, starting with analyzing current vulnerabilities and recommending/implementing improvements across networks and systems. Learners will research and apply relevant security measures, develop a vulnerability testing process, and create an incident response plan. Crucially, they'll produce detailed developer documentation to ensure secure and efficient development practices for the Java/SpringBoot backend, RabbitMQ, Thymeleaf, and htmx frontend, all hosted on AWS. The project emphasizes maintaining Hinna's core principles of simplicity, speed, and security, encouraging innovative solutions that balance these aspects. Mentorship will be provided by the product owner, who will either also serve as the project manager or offer more direct guidance in its absence, ensuring regular progress reviews and support.
Work Experience
To showcase my professional journey, highlighting relevant experiences that align with my cybersecurity aspirations and skills development.
Capstone Project – Completed June 2024
A comprehensive cybersecurity assessment of Premium House Lights Inc. (PHL) revealed critical vulnerabilities in their network infrastructure, leaving them susceptible to cyberattacks. To address these risks, a detailed report was prepared, recommending a multi-faceted approach to enhance PHL's cybersecurity posture. Key recommendations include implementing robust network segmentation, upgrading firewall technology, strengthening access controls, securing wireless networks, and establishing a rigorous patch management process. Additionally, the report emphasizes proactive security monitoring, incident response planning, and employee security awareness training. By implementing these measures, PHL can significantly bolster its resilience against cyber threats, safeguarding its assets, reputation, and customer data.


