Capstone Project
The final project combines the tools, skills and techniques that you have seen throughout the course. You will be given a realistic on-the-job scenario, from which you will make security recommendations. Once you have completed your recommendations, you will analyze a threat scenario and create an incident response report. As a final step, you will prepare a presentation for Demo Day to outline key features of your recommendations and report, and showcase your work
You will take a look at the Equifax Data Breach in two parts:
Equifax Data Breach Post Mortem
Actions Taken by Equifax and Federal Agencies in Response to the 2017 Breach
Case Study 1
Reflection Questions
What were the primary reasons Equifax failed at detecting and responding to the incident?
What best practices weren’t followed by Equifax that could have prevented this incident from happening?
On a tactical level, how would you prioritize the work required to address the identified gaps in processes and systems?
Company Scenario
In this step, you’ll read through the company profile that you will use throughout your project. This scenario will provide essential context for your work as you move forward.
Write an Email Report to your Manager
Based on the company scenario, you’ll write a report to your manager with specific recommendations for the company’s security. This task consolidates knowledge from previous assignments. Guidelines for the key points will be available in Compass.
The Threat Scenario
Now that you’ve considered the company’s security needs, it’s time to test them. You will be given a simulated threat scenario based on the company profile. The scenario will include relevant artifacts to help you analyze the attack.
Case Study 1 - Submission
SHA256: c8695cb379fb5c88ac8efaa0b2fe4f5c44d562fd1fe1332e3dd0e1885d49d63a
MD5: f8699e803d4d036d3db5eeba04e61ffc
As preparation for your final project, you will examine a few case studies of Cyber Security incidents, along with supporting reports and documentation. Use the discussion questions included with each case study to guide your reading and notes. This will help guide discussions with your peers, and better prepare you for your project work.
You will take a look at the Target Data Breach in two parts:
Target Data Breach Post Mortem
A “Kill Chain” Analysis of the 2013 Target Data Breach
Case Study 2
Reflection Questions
What are some steps you think would be useful for a company like Target to follow in order to reduce their third-party risks?
What are the top five criteria by which you would measure a third party’s security posture before deciding to onboard them into your company’s networks?
What are the best practices a company like Target should follow to make a hacker's life harder when attempting to perform lateral movement within an internal network?
Incident Response Report
The majority of your time on this project will be spent on this step. You will analyze the artifacts and threat scenario and, using this information, create an incident response report tailored for your manager. Many of these tasks will be familiar from previous coursework and you will find guidelines of key points on Compass. Be sure to dedicate time for the analysis of the artifacts.
Analyze an organization and its tolerance for risk
Assess an organization's vulnerabilities and the threats that it faces
Assess and apply risk management processes
Recommend improvements for the company's security posture, including policy enhancements.
Recommend indicators of compromise (IoCs) tailored to the organization's needs and the identified threats
Recommend steps for completing an incident response
Recommend remediation actions for discovered vulnerabilities based on industry-standard frameworks and resources.
Make recommendations to improve security posture
Core Competencies
Decision-making competence: appropriate analysis, response, and process to successfully meet the Cyber Security needs for the selected target situation.
Tools and frameworks: appropriate selection of tools and frameworks for appropriate completion of project tasks, including relevant rationale.
Communication skills: appropriate documentation throughout the project, including policy and playbook design, and engaging presentation.
Problem-solving skills: ability to apply selected tools and frameworks to a threat situation, and determine its relative success.
Continuous learning: ability to reflect on the strengths and challenges of project completion, and identify areas for future development and iteration.
Incident Response Report - Submission
SHA256: 1c637b20078ccb162ebb520075790b7bc9acd60ec5da2260e8c1a5884dd8c6fa
MD5: f266216eafb17a4d8160ef0e21ed2e88
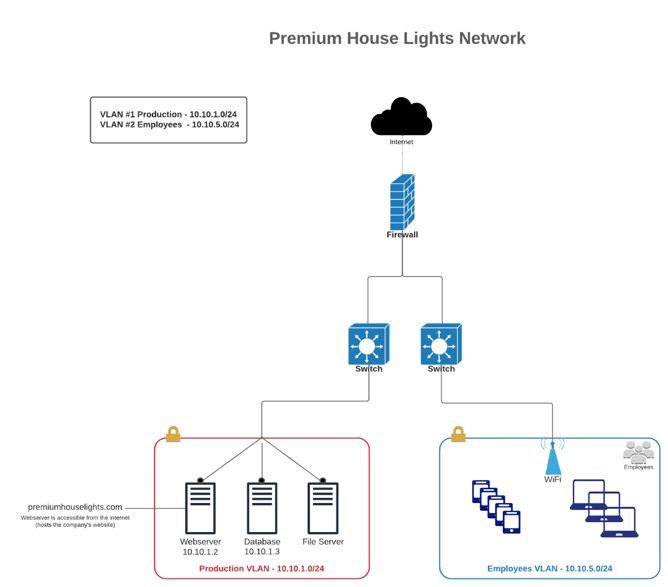
PHL Network Topology
There are a lot of possible topics of discussion in this project. To ensure you are able to speak in detail within the 5 minute timeframe, you will choose one of the topics listed below to focus on for your presentation.
Chosen Topic - Command & Control: Lateral Movement
The Final Presentation
Presentation Slideshow
Video Presentation